Peppol PKI explained
This article outlines the details of the Peppol PKI. It shows how the PKI is structured and where it is used. See the page on Peppol Certificate update for the specifics on this process.
OpenPeppol PKI G3 (v4) - since 2025
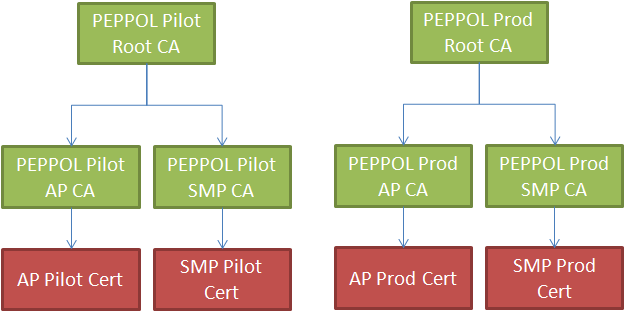
The PKI is called "OpenPeppol PKI G3" and the root certificates are valid from 2025 to 2035. The "G3" stems from the fact, that this is the third generation of OpenPeppol certificates hosted with Digicert. Previously there was another PKI in place which was the fourth version. The structure is similar to the previous G2 (v3) one and looks like this:
The migration from G2 to G3 was completed in Q1 2026. No new G2 certificates are issued since March 2026.
The root certificates are available for download in OpenPeppol Confluence. Predefined Peppol truststores in PKCS12 format are available at https://github.com/phax/peppol-commons/tree/master/peppol-commons/src/main/resources/truststore for AP and SMP separate for Test and Production Peppol Network. Note: no complete truststore is provided, as it is deemed insecure to trust test messages in production and vice versa.
For details and further information, please see the Peppol PKI 2025 - Certificate Authority Migration Plan and the Peppol PKI 2025 - Issuing and Enrolment Process pages.
OpenPeppol PKI G2 (v3) - 2018 to 2026 (deprecated)
The previous PKI generation "OpenPeppol PKI v3" (G2) was in use from 2018 to early 2026. It was replaced by the G3 PKI described above. No new G2 certificates are issued since March 2026.
Certificate usage in Peppol
This section tries to give a rough overview where certificates are used for what purpose.
-
SMP Server
-
Uses the Peppol SMP certificate to sign responses to
SignedServiceMetadatarequests (as inhttps://smp.example.org/{participantID}/services/{docTypeID}) - Uses the Peppol SMP certificate as a client certificate when communicating with the SML (for service group creation and deletion)
- Requires the public part of the Peppol AP certificate for usage in the public endpoints (the information that is queried from the outside).
- Optionally uses the Peppol SMP certificate as a client certificate when communicating with the Peppol Directory (for business card updates and deletions)
-
Uses the Peppol SMP certificate to sign responses to
-
SMP Client
- Verifies that the response from the SMP server was signed by a valid Peppol SMP certificate
-
AP Server (receiving documents)
- Requires a SSL/TLS certificate for https usage. This SSL/TLS certificate is NOT issued by OpenPeppol but must be issued by a trusted third party. This SSL/TLS certificate should not be self-signed!
- Verifies that the incoming document was signed with a Peppol AP certificate.
-
AP Client (sending documents)
- Signs the AS4 message with the Peppol AP certificate. Includes the public part of the certificate inside the AS4 message.
-
SMK/SML
- The SMK requires requests to contain an SMP Pilot Certificate to perform writing operations (mTLS)
- The SML requires requests to contain an SMP Production Certificate to perform writing operations (mTLS)
-
Peppol Directory
- The test Peppol Directory requires requests to contain an SMP Pilot Certificate to perform writing operations (mTLS)
- The production Peppol Directory requires requests to contain an SMP Production Certificate to perform writing operations (mTLS)